Windows LAPS: Create local administrator account via Microsoft Intune
When deploying LAPS in your environment you might want to disable the build in local administrator account and create a custom one. Previously with legacy LAPS this was possible during installation with CUSTOMADMINNAME parameter, for example:
msiexec /q /i LAPS.x64.msi CUSTOMADMINNAME=HulkWindows LAPS with Microsoft Entra ID now Generally Available!
As Windows LAPS is now build-in directly to supported editions, there is no need for installation, resulting in the absence of the local administrator creation feature.
However, this doesn't mean you can't achieve similar functionality through other means. I personally prefer utilizing the Microsoft Intune Remediations feature as it allows managing local accounts effectively with PowerShell Scripts.
The first step in process involves detecting the presence of a specific user on the target machine. In this example, I’m focusing on detecting the existence of the user "Hulk." This can be achieved using PowerShell, and here's how the detection script might look:
$targetUser = "Hulk"
$existingUser = Get-LocalUser -Name $targetUser -ErrorAction SilentlyContinue
if ($existingUser) {
Write-Host "User '$targetUser' exists."
exit 0 # Exit with code 0 to indicate success
} else {
Write-Host "User '$targetUser' does not exist."
exit 1 # Exit with code 1 to indicate failure
}In this script, I’m using the Get-LocalUser cmdlet to check if the specified user exists on the machine. If the user is found, the script exits with a success code (0); otherwise, it exits with a failure code (1).
Now, let's move on to the remediation script. If the user doesn't exist, we want to create and enable the user account. The script below accomplishes this by generating a random password, creating the user account, and setting up appropriate account settings:
function Generate-RandomPassword {
param (
[int]$length
)
$validChars = 'abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789!@#$%^&*()_+-=[]{}|;:,.<>?'
$password = ''
1..$length | ForEach-Object {
$randomChar = Get-Random -Minimum 0 -Maximum $validChars.Length
$password += $validChars[$randomChar]
}
return $password
}
$targetUser = "Hulk"
# Check if the user already exists
$existingUser = Get-LocalUser -Name $targetUser -ErrorAction SilentlyContinue
if (!$existingUser) {
# Create the user account with temporary password and enable it
$password = Generate-RandomPassword 14 # Generate a random password
$securePassword = ConvertTo-SecureString $password -AsPlainText -Force
New-LocalUser -Name $targetUser -Password $securePassword -AccountNeverExpires -UserMayNotChangePassword -PasswordNeverExpires
Enable-LocalUser -Name $targetUser
Write-Host "User '$targetUser' created and enabled with a temporary password."
exit 0 # Exit with code 0 to indicate success
} else {
Write-Host "User '$targetUser' already exists. No remediation needed."
exit 1 # Exit with code 1 to indicate failure
}This script generates a strong, temporary password using the Generate-RandomPassword function. Then, if the user doesn't already exist, it creates the user account with the generated password and enables the account. If the user already exists, the script indicates that no remediation is needed.
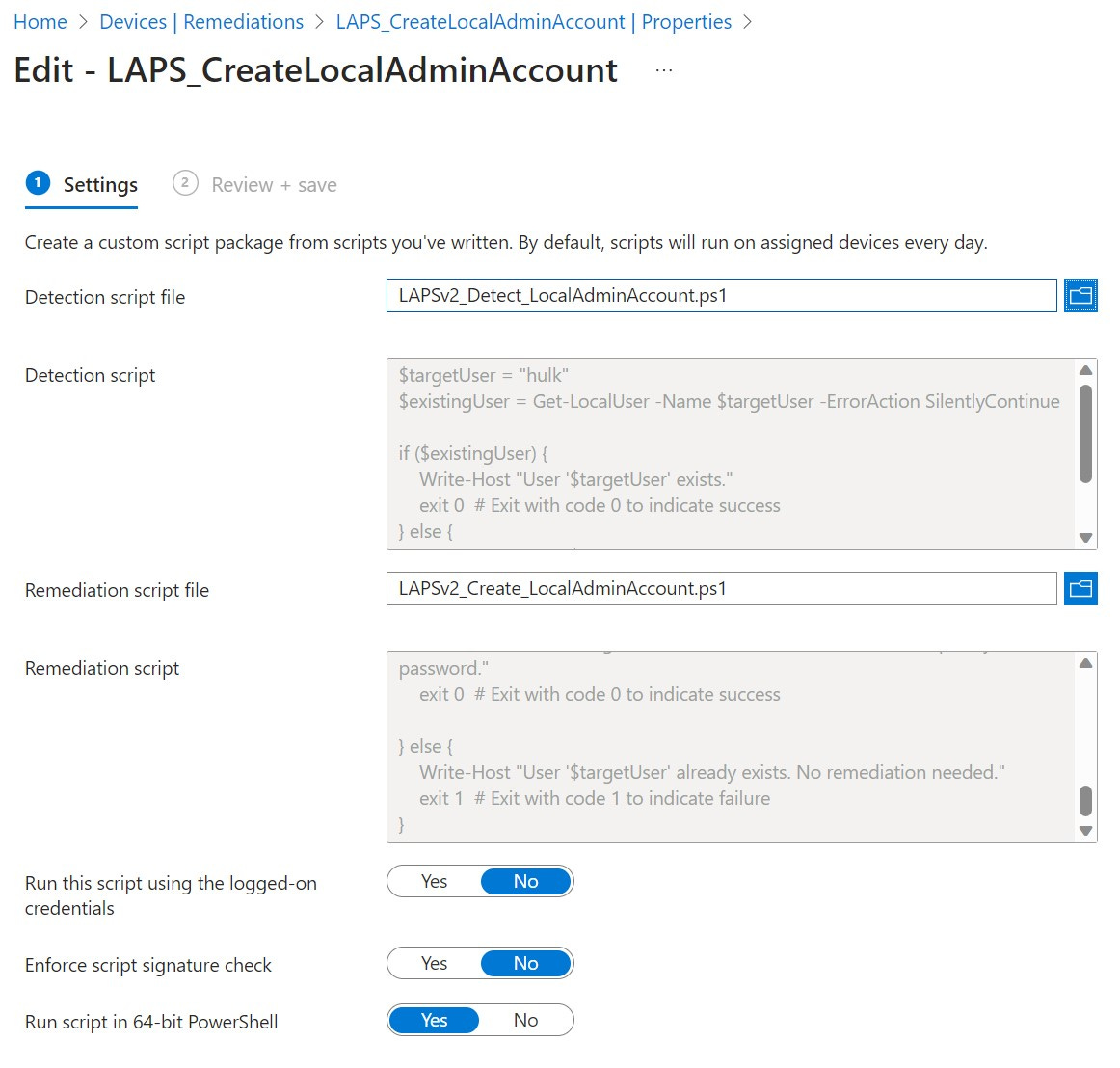
Create a script package in Microsoft Intune > Devices > Remediations.
Make sure to select Run script in 64-bit PowerShell.
NOTE: Created user is NOT added to local administrators group automatically.
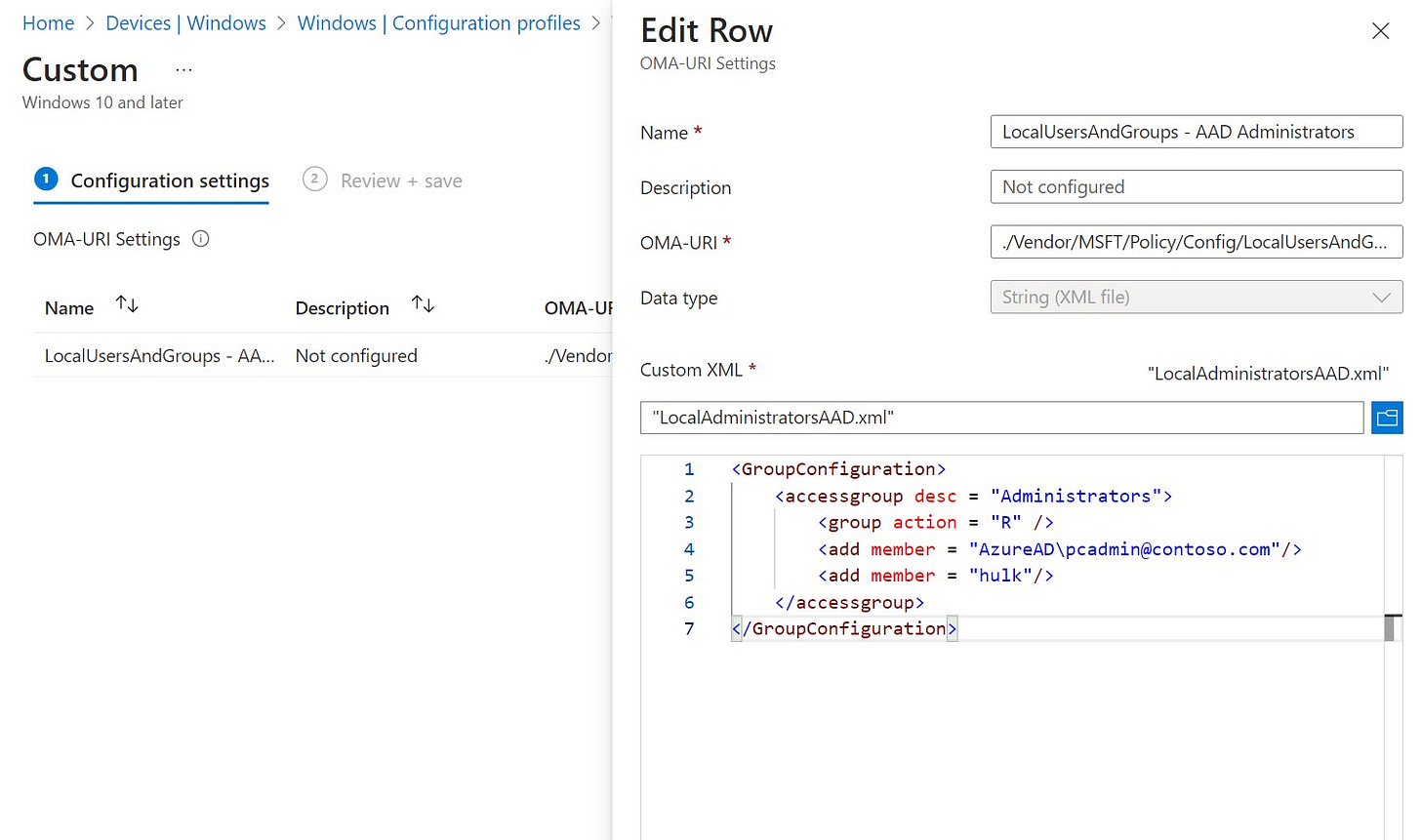
The final step is to add the created user to local administrators group. I’m doing that with Custom OMA-URI Setting:
./Vendor/MSFT/Policy/Config/LocalUsersAndGroups/Configure
<GroupConfiguration>
<accessgroup desc = "Administrators">
<group action = "R" />
<add member = "AzureAD\pcadmin@contoso.com"/>
<add member = "hulk"/>
</accessgroup>
</GroupConfiguration>By combining these two scripts and deploying them through Microsoft Intune's remediation feature, you can effectively manage local user accounts across your environment. This approach not only provides the flexibility to create custom accounts but also allows for automation and consistency in user account management.
Now we can configure Windows LAPS with custom managed local administrator account.