Switching Off Self-Service Password Reset for Administrators in Microsoft Entra
Recently, I assisted a client in implementing the Microsoft Entra self-service password reset (SSPR) feature. Their requirement was that this service be enabled only for non-privileged accounts. The policy was tied to a user group which did not include administrative accounts; however, SSPR was still operational for administrative accounts. This experience is expected as it is by default permitted to reset passwords for administrative roles such as Global Administrator, Exchange Administrator, Intune Administrator, Security Administrator, etc.
A two-gate policy is enabled which mandates two forms of authentication evidence (e.g., entering a code from the Microsoft Authenticator app plus an SMS code). While the two-gate policy offers significant protection, it is still possible to disable the default policy to prevent administrators from changing their own passwords using the Update-MgPolicyAuthorizationPolicy PowerShell cmdlet.
First, the Microsoft.Graph.Identity.SignIns Module must be installed. Use the following command to install this package via PowerShellGet:
Install-Module -Name Microsoft.Graph.Identity.SignInsOnce the module is installed, it should be imported, and the Connect-MgGraph cmdlet must be invoked before executing any commands that interact with Microsoft Graph. This cmdlet retrieves the access token through the Microsoft Authentication Library.
Import-Module Microsoft.Graph.Identity.SignIns
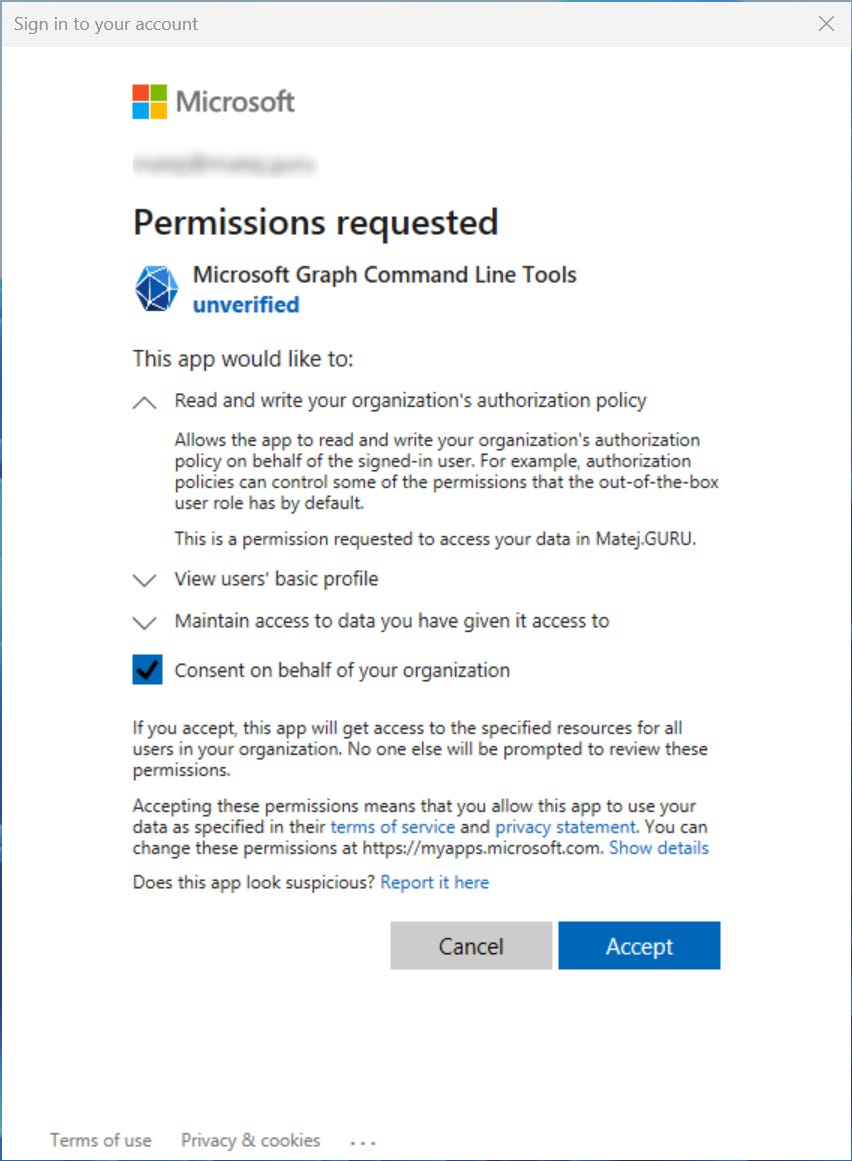
Connect-MgGraph -Scopes Policy.ReadWrite.AuthorizationIf you haven't already, you will need to provide consent for Microsoft Graph.
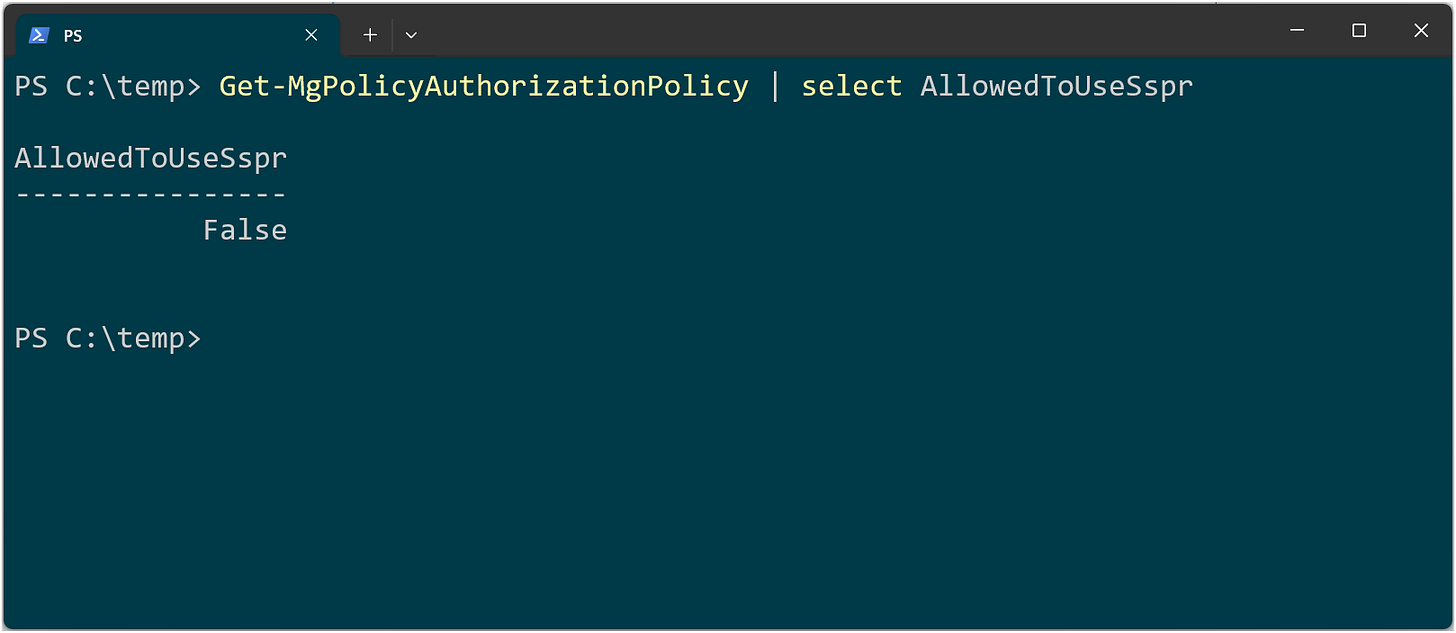
Once connected, we can check the current setting for AllowedToUseSspr, which shows whether administrators of the tenant are permitted to use the SSPR.
Get-MgPolicyAuthorizationPolicy | select AllowedToUseSsprTo disable SSPR for administrators, we need to set the value to FALSE.
$params = @{
allowedToUseSSPR = $false
}
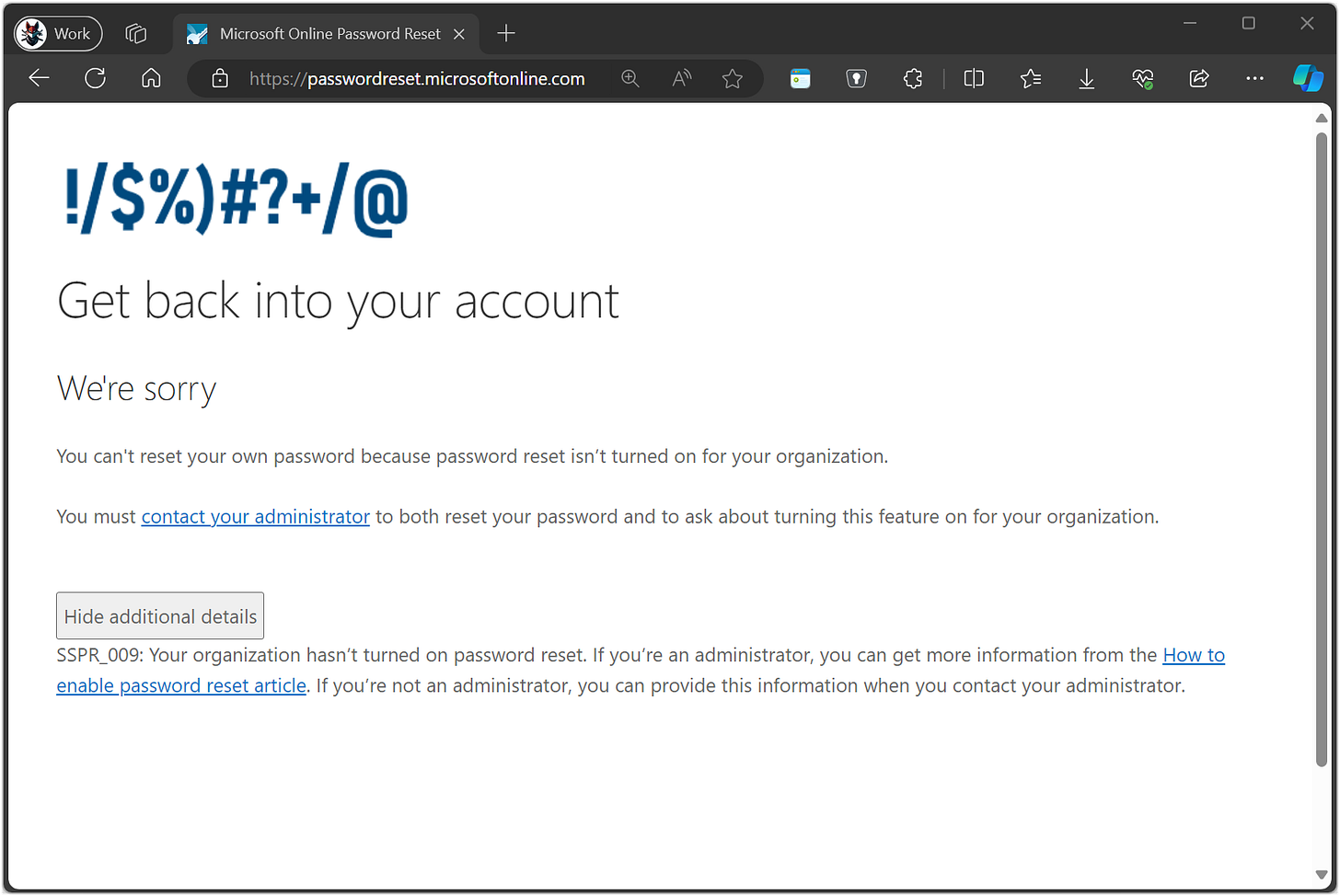
Update-MgPolicyAuthorizationPolicy -BodyParameter $paramsThe policy takes effect within 60 minutes. Our test confirms that the administrator indeed cannot use the SSPR service anymore.
I hope you find this information useful for improving your administrator’s security.